New research uncovers that Android lock patterns are easily predictable
It
is indeed surprising to know that most of the Android lock patterns are
predictable because people generally use the most common combinations.
Google introduced the
Android Lock Patterns (ALPs) or password alternative in 2008, when it introduced its Android Operating system.
In
Android’s lock-screen pattern system, users just need to draw some
lines in between the nodes instead of typing any password or PIN. Hence,
it is much easier to remember and use them in comparison to the
passwords.
However, Marte Løge, a graduate of the
Norwegian University of Science and Technology conducted a study on around 4,000 lock patterns. Surprisingly, her study revealed these
patterns are pretty easy to guess and chances are that we are using one of these easy ALPs.
This
study was a part of her master’s thesis and she discovered that there
were some bad practices which were commonly being used while applying
these patterns.
Last week Løge gave a presentation on the topic
“Tell Me Who You Are, and I Will Tell You Your Lock Pattern” which was
held at the at the PasswordsCon conference in Las Vegas. Then, she told
Ars Technica
that ‘humans are predictable’, she continued “We’re seeing the same
aspects used when creating a pattern locks [as are used in]pin codes and
alphanumeric passwords.”
Basically, ALPs would involve a minimum of four nodes and a maximum of nine rounding up to a total of 389,112 possible patterns.
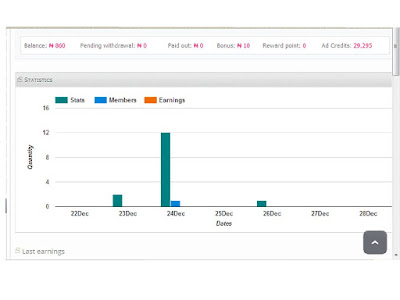
Here’s the breakdown:
| LENGTH | NUMBER OF COMBINATIONS |
|---|
| 4 | 1,624 |
| 5 | 7,152 |
| 6 | 26,016 |
| 7 | 72,912 |
| 8 | 140,704 |
| 9 | 140,704 |
Her
findings revealed some interesting facts, she found that the patterns
which started at the uppermost left node of the screen comprised of
almost 44 percent of these patterns. Those which started from one of the
four corner nodes made up of 77 percent of the patterns.
It was observed that users usually used around five nodes which would result in to around 9000 predictable pattern combinations.
Most
common patterns just used four nodes and this reduces the possibility
of common combinations to just 1,624 making it easy to be guessed.
The
most commonly used patterns comprised of moving from left to right and
top to bottom, further making it easy to guess the pattern.
Her
study also indicated that males and females have a tendency to create
patterns in some distinct and predictable ways. She observed that both
the sexes preferred using a nine-nodes pattern most of the times and
very rarely used the eight nodes pattern though both these provided
almost the same number of possible options of patterns.
Her
findings also revealed that irrespective of their gender, the starting
places used by left handed were similar to their right handed
counterparts.
Løge says that it is not only the number of nodes
used in the ALPs, but also the specific sequence of the nodes used in
the pattern which helps to guess the sequence of the pattern. She
explained this by giving an example, “Assigning the nine nodes the same
digits found on a standard phone interface, the combination 1, 2, 3, 6
will receive a lower complexity score than the combination 2, 1, 3, 6,
since the latter pattern changes direction.”
She also discovered
that in comparison, males use more complex patterns such as 2,3,1
sequence and females hardly prefer to use the crossovers.

In case of password breaches, it was found that most common password cracked were “1234567” and “letmein”.
Løge,
says that similar to the passwords, ALPs too have similar weakness, she
found that almost 10 percent of the patterns took the shape of the
alphabetic letter that corresponded to the first initial of user’s name
or their spouse or child or any other person who is pretty close to the
user. This indicated that there is one-in-ten chance that attacker can
predict the ALP. Suppose, attacker knows the names of the victim or
their people it becomes all the more easier guess.
“It was a
really fun thing to see that people use the same type of strategy for
remembering a pattern as a password,” Løge said. “You see the same type
of behavior.”
Løge says that by collecting a huge number of ALPs
it is possible to build “Markov model” which can help attackers to
predict the ALPs.
Ways to make the ALPs better and attack proof:
Løge told
Ars Technica, that there are ways to make these pattern passwords better and also provided some tips to help users.
Løge
says that it is essential to use a whole bunch of nodes and always aim
to make a pattern crossover itself a bunch which is difficult to make
out from a distance.
She also advises that users need to switch off the “show pattern” by going in the security settings of their phone’s device.
One more important tip is to stop starting the pattern from top left node.
Now
that readers have understood the dangers of using the common pattern
locks, do try to make your ALPs more complex and use crossovers to avoid
being attacked by some crook.